Generate New Ssh Key Cisco
- October 2, 2015
- Posted by: Syed Shujaat
- Category: Cisco, Networking Solutions
- Ssh Key Setup
- Generate Ssh Key Cisco Router
- Ssh Key Generation
- Generate New Ssh Key Cisco Password
- Generate New Ssh Key Mac
- Generate Ssh Key Linux
Nov 23, 2011 crypto key generate rsa label ssh modulus 1024. The name for the keys will be: ssh% The key modulus size is 1024 bits% Generating 1024 bit RSA keys, keys will be non-exportable. OK (elapsed time was 3 seconds) This alone should make sure that the SSH is able to run in SSHv2.
Use this command to generate RSA key pairs for your Cisco device (such as a router). keys are generated in pairs–one public RSA key and one private RSA key.
If your router already has RSA keys when you issue this command, you will be warned and prompted to replace the existing keys with new keys.
- Solved: Hello, I am trying to change the key for SSH from 1024 to 2048 but I have (so far) no solution for that. Unfortunately, ip ssh rsa keypair-name SSH and crypto key generate rsa general-keys modulus 2048 label SSH don't work. I trying also.
- Mar 31, 2018 Generate public key and store into a file. It is a simple one liner command to generate a public key from a private key, so lets say our private key is named ‘user@myserver.key’ and we want to generate the public key and name it ‘authorizedkeys’. Below is the command to do this.
NOTE: Before issuing this command, ensure that your router has a hostname and IP domain name configured (with the hostname and ipdomain-name commands).
You will be unable to complete the cryptokeygeneratersacommand without a hostname and IP domain name. (This situation is not true when you generate only a named key pair.)
Here are the steps to Enable SSH and Crypto Key setup : 2 config must requried for SSH
1 Setup Local VTY line User ID and password
router (Config) # Line VTY 0 15
router (Config-line)# login local
router (Config-line)# Exit
!!! create local login ID/Pass
router (Config)# username [loginid] password [cisco]
router (Config)# username loginid1 password cisco1
2. router (Config)# ip domain-name example.com
router (Config)# crypto key generate rsa
how many bits in the modulus [512] :1024
router (Config)# ip ssh version2
router (Config)# CTRL Z
Note | Secure Shell (SSH) may generate an additional RSA key pair if you generate a key pair on a router having no RSA keys. The additional key pair is used only by SSH and will have a name such as {router_FQDN }.server. For example, if a router name is “router1.cisco.com,” the key name is “router1.cisco.com.server.” |
This command is not saved in the router configuration; however, the RSA keys generated by this command are saved in the private configuration in NVRAM (which is never displayed to the user or backed up to another device) the next time the configuration is written to NVRAM.
Modulus Length
When you generate RSA keys, you will be prompted to enter a modulus length. The longer the modulus, the stronger the security. However, a longer modules take longer to generate (see the table below for sample times) and takes longer to use.
The size of Key Modulus range from 360 to 2048. Choosing modulus greater than 512 will take longer time.
| Router | 360 bits | 512 bits | 1024 bits | 2048 bits (maximum) |
|---|---|---|---|---|
| Cisco 2500 | 11 seconds | 20 seconds | 4 minutes, 38 seconds | More than 1 hour |
| Cisco 4700 | Less than 1 second | 1 second | 4 seconds | 50 seconds |
Cisco IOS software does not support a modulus greater than 4096 bits. A length of less than 512 bits is normally not recommended. In certain situations, the shorter modulus may not function properly with IKE, so we recommend using a minimum modulus of 2048 bits.
Syntax Description : Optional Strings to embed with SSH Crypto key
| general-keys | (Optional) Specifies that a general-purpose key pair will be generated, which is the default. | ||
| usage-keys | (Optional) Specifies that two RSA special-usage key pairs, one encryption pair and one signature pair, will be generated. | ||
| signature | (Optional) Specifies that the RSA public key generated will be a signature special usage key. | ||
| encryption | (Optional) Specifies that the RSA public key generated will be an encryption special usage key. | ||
| labelkey-label | (Optional) Specifies the name that is used for an RSA key pair when they are being exported.If a key label is not specified, the fully qualified domain name (FQDN) of the router is used. | ||
| exportable | (Optional) Specifies that the RSA key pair can be exported to another Cisco device, such as a router. | ||
| modulusmodulus-size | (Optional) Specifies the IP size of the key modulus.By default, the modulus of a certification authority (CA) key is 1024 bits. The recommended modulus for a CA key is 2048 bits. The range of a CA key modulus is from 350 to 4096 bits.
| ||
| storagedevicename: | (Optional) Specifies the key storage location. The name of the storage device is followed by a colon (:). | ||
| redundancy | (Optional) Specifies that the key should be synchronized to the standby CA. | ||
| ondevicename: | (Optional) Specifies that the RSA key pair will be created on the specified device, including a Universal Serial Bus (USB) token, local disk, or NVRAM. The name of the device is followed by a colon (:).Keys created on a USB token must be 2048 bits or less. |
| Command | Description |
|---|---|
| copy | Copies any file from a source to a destination, use the copy command in privileged EXEC mode. |
| cryptokeystorage | Sets the default storage location for RSA key pairs. |
| debugcryptoengine | Displays debug messages about crypto engines. |
| hostname | Specifies or modifies the hostname for the network server. |
| ipdomain-name | Defines a default domain name to complete unqualified hostnames (names without a dotted-decimal domain name). |
| showcryptokeymypubkeyrsa | Displays the RSA public keys of your router. |
| show crypto pki certificates | Displays information about your PKI certificate, certification authority, and any registration authority certificates. |
Contents
Introduction
Secure Shell (SSH) is a protocol which provides a secure remote access connection to network devices. Communication between the client and server is encrypted in both SSH version 1 and SSH version 2. Implement SSH version 2 when possible because it uses a more enhanced security encryption algorithm.
This document discusses how to configure and debug SSH on Cisco routers or switches that run a version of Cisco IOS® Software that supports SSH. This document contains more information on specific versions and software images.
Prerequisites
Requirements
The Cisco IOS image used must be a k9(crypto) image in order to support SSH. For example c3750e-universalk9-tar.122-35.SE5.tar is a k9 (crypto) image.
Components Used
The information in this document is based on Cisco IOS 3600 Software (C3640-IK9S-M), Release 12.2(2)T1.
SSH was introduced into these Cisco IOS platforms and images:
SSH Version 1.0 (SSH v1) server was introduced in some Cisco IOS platforms and images that start in Cisco IOS Software Release 12.0.5.S.
SSH client was introduced in some Cisco IOS platforms and images starting in Cisco IOS Software Release 12.1.3.T.
SSH terminal-line access (also known as reverse-Telnet) was introduced in some Cisco IOS platforms and images starting in Cisco IOS Software Release 12.2.2.T.
SSH Version 2.0 (SSH v2) support was introduced in some Cisco IOS platforms and images starting in Cisco IOS Software Release 12.1(19)E.
Refer to How to Configure SSH on Catalyst Switches Running CatOS for more information on SSH support in the switches.
Refer to the Software Advisor (registered customers only) for a complete list of feature sets supported in different Cisco IOS Software releases and on different platforms.
The information presented in this document was created from devices in a specific lab environment. All of the devices used in this document started with a cleared (default) configuration. If you are in a live network, make sure that you understand the potential impact of any command before you use it.
Conventions
Refer to Cisco Technical Tips Conventions for more information on document conventions.
SSH v1 vs. SSH v2
Use the Cisco Software Advisor (registered customers only) in order to help you find the version of code with appropriate support for either SSH v1 or SSH v2.
Network Diagram
Test Authentication
Authentication Test without SSH
First test the authentication without SSH to make sure that authentication works with the router Carter before you add SSH. Authentication can be with a local username and password or with an authentication, authorization, and accounting (AAA) server that runs TACACS+ or RADIUS. (Authentication through the line password is not possible with SSH.) This example shows local authentication, which lets you Telnet into the router with username 'cisco' and password 'cisco.'
Authentication Test with SSH
In order to test authentication with SSH, you have to add to the previous statements in order to enable SSH on Carter and test SSH from the PC and UNIX stations.
At this point, the show crypto key mypubkey rsa command must show the generated key. After you add the SSH configuration, test your ability to access the router from the PC and UNIX station. If this does not work, see the debug section of this document.
Optional Configuration Settings
Prevent Non-SSH Connections
If you want to prevent non-SSH connections, add the transport input ssh command under the lines to limit the router to SSH connections only. Straight (non-SSH) Telnets are refused.
Test to make sure that non-SSH users cannot Telnet to the router Carter.
Set Up an IOS Router or Switch as SSH Client
There are four steps required to enable SSH support on a Cisco IOS router:
Configure the hostname command.
Configure the DNS domain.
Generate the SSH key to be used.
Enable SSH transport support for the virtual type terminal (vtys).

If you want to have one device act as an SSH client to the other, you can add SSH to a second device called Reed. These devices are then in a client-server arrangement, where Carter acts as the server, and Reed acts as the client. The Cisco IOS SSH client configuration on Reed is the same as required for the SSH server configuration on Carter.
Issue this command to SSH from the Cisco IOS SSH client (Reed) to the Cisco IOS SSH server (Carter) in order to test this:
SSH v1:
SSH v2:
Setup an IOS Router as an SSH server that performs RSA based User Authentication
Complete these steps in order to configure the SSH server to perform RSA based authentication.
Specify the Host name.
Define a default domain name.
Generate RSA key pairs.
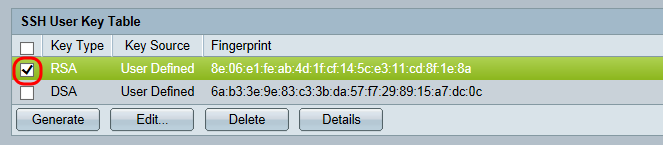
Configure SSH-RSA keys for user and server authentication.
Configure the SSH username.
Specify the RSA public key of the remote peer.
Specify the SSH key type and version. (optional)
Exit the current mode and return to privileged EXEC mode.
Note: Refer to Secure Shell Version 2 Support for more information.
Add SSH Terminal-Line Access
If you need outbound SSH terminal-line authentication, you can configure and test SSH for outbound reverse Telnets through Carter, which acts as a comm server to Philly.
If Philly is attached to Carter's port 2, then you can configure SSH to Philly through Carter from Reed with the help of this command:
SSH v1:
SSH v2:
You can use this command from Solaris:
Restrict SSH access to a subnet
You need to limit SSH connectivity to a specific subnetwork where all other SSH attempts from IPs outside the subnetwork should be dropped.
You can use these steps to accomplish the same:
Define an access-list that permits the traffic from that specific subnetwork.
Restrict access to the VTY line interface with an access-class.
This is an example configuration. In this example only SSH access to the 10.10.10.0 255.255.255.0 subnet is permitted, any other is denied access.
Note: The same procedure to lock down the SSH access is also applicable on switch platforms.
Configure the SSH Version
Configure SSH v1:
Configure SSH v2:
Configure SSH v1 and v2:
Note: You receive this error message when you use SSHv1:
Ssh Key Setup
Note: Cisco bug ID CSCsu51740 (registered customers only) is filed for this issue. Workaround is to configure SSHv2.
Variations on banner Command Output
The banner command output varies between the Telnet and different versions of SSH connections. This table illustrates how different banner command options work with various types of connections.
| Banner Command Option | Telnet | SSH v1 only | SSH v1 and v2 | SSH v2 only |
|---|---|---|---|---|
| banner login | Displayed before logging into the device. | Not displayed. | Displayed before logging into the device. | Displayed before logging into the device. |
| banner motd | Displayed before logging into the device. | Displayed after logging into the device. | Displayed after logging into the device. | Displayed after logging into the device. |
| banner exec | Displayed after logging into the device. | Displayed after logging into the device. | Displayed after logging into the device. | Displayed after logging into the device. |
Unable to Display the Login Banner
SSH version 2 supports the login banner. The login banner is displayed if the SSH client sends the username when it initiates the SSH session with the Cisco router. For example, when the Secure Shell ssh client is used, the login banner is displayed. When the PuTTY ssh client is used, the login banner is not displayed. This is because Secure Shell sends the username by default and PuTTY does not send the username by default.
The Secure Shell client needs the username to initiate the connection to the SSH enabled device. The Connect button is not enabled if you do not enter the host name and username. This screenshot shows that the login banner is displayed when Secure Shell connects to the router. Then, the login banner password prompt displays.
The PuTTY client does not require the username to initiate the SSH connection to the router. This screenshot shows that the PuTTY client connects to the router and prompts for the username and password. It does not display the login banner.
This screen shot shows that the login banner is displayed when PuTTY is configured to send the username to the router.
debug and show Commands
Before you issue the debug commands described and illustrated here, refer to Important Information on Debug Commands. Certain show commands are supported by the Output Interpreter Tool (registered customers only) , which allows you to view an analysis of show command output.
debug ip sshâDisplays debug messages for SSH.
show sshâDisplays the status of SSH server connections.
show ip sshâDisplays the version and configuration data for SSH.
Version 1 Connection and no Version 2
Version 2 Connection and no Version 1
Version 1 and Version 2 Connections
Sample Debug Output
Router Debug
Note: Some of this good debug output is wrapped to multiple lines because of spatial considerations.
Server Debug
Note: This output was captured on a Solaris machine.
What can go Wrong
These sections have sample debug output from several incorrect configurations.
Generate Ssh Key Cisco Router
SSH From an SSH Client Not Compiled with Data Encryption Standard (DES)
Solaris Debug
Router Debug
Bad Password
Ssh Key Generation
Router Debug
SSH Client Sends Unsupported (Blowfish) Cipher
Router Debug
Geting the '%SSH-3-PRIVATEKEY: Unable to retrieve RSA private key for' Error
If you receive this error message, it may be caused due to any change in the domain name or host name. In order to resolve this, try these workarounds.
Zeroize the RSA keys and re-generate the keys.
If the previous workaround does not work, try these steps:
Zeroize all RSA keys.
Reload the device.
Create new labeled keys for SSH.
Cisco bug ID CSCsa83601 (registered customers only) has been filed to address this behaviour.
Generate New Ssh Key Cisco Password
Troubleshooting Tips
Generate New Ssh Key Mac
If your SSH configuration commands are rejected as illegal commands, you have not successfully generated a RSA key pair for your router. Make sure you have specified a host name and domain. Then use the crypto key generate rsa command to generate an RSA key pair and enable the SSH server.
When you configure the RSA key pair, you might encounter these error messages:
No hostname specified
You must configure a host name for the router using the hostname global configuration command.
No domain specified
You must configure a host domain for the router using the ip domain-name global configuration command.
The number of allowable SSH connections is limited to the maximum number of vtys configured for the router. Each SSH connection uses a vty resource.
Generate google map api key v3. SSH uses either local security or the security protocol that is configured through AAA on your router for user authentication. When you configure AAA, you must ensure that the console is not running under AAA by applying a keyword in the global configuration mode to disable AAA on the console.
No SSH server connections running.
This output suggests that the SSH server is disabled or not enabled properly. If you have already configured SSH, it is recommended that you reconfigure the SSH server in the device. Complete these steps in order to reconfigure SSH server on the device.
Delete the RSA key pair. After the RSA key pair is deleted, the SSH server is automatically disabled.
Note: It is important to generate a key-pair with at least 768 as bit size when you enable SSH v2.
Caution: This command cannot be undone after you save your configuration, and after RSA keys have been deleted, you cannot use certificates or the CA or participate in certificate exchanges with other IP Security (IPSec) peers unless you reconfigure CA interoperability by regenerating RSA keys, getting the CA's certificate, and requesting your own certificate again.Refer to crypto key zeroize rsa - Cisco IOS Security Command Reference, Release 12.3 for more information on this command.
Reconfigure the hostname and domain name of the device.
Generate an RSA key pair for your router, which automatically enables SSH.
Refer to crypto key generate rsa - Cisco IOS Security Command Reference, Release 12.3 for more information on the usage of this command.
Note: You can receive the SSH2 0: Unexpected mesg type received error message due to a packet received that is not understandable by the router. Increase the key length while you generate rsa keys for ssh in order to resolve this issue.
Configure SSH server. In order to enable and configure a Cisco router/switch for SSH server, you can configure SSH parameters. If you do not configure SSH parameters, the default values are used.
ip ssh {[timeout seconds] [authentication-retries integer]}Refer to ip ssh - Cisco IOS Security Command Reference, Release 12.3 for more information on the usage of this command.