Elliptic Curve Key Generation Algorithm
- Elliptic Curve Key Generation Algorithm Worksheet
- Elliptic Curve Key Length
- Elliptic Curve Key Generation Algorithm Download
- Elliptic Curve Cryptography
The blind brute force algorithm (pick private key = 1, test, if not the right pub key then increment private key and try again) would work, although the best known algorithm to solve the Elliptic Curve DLP takes roughly O(n^(1/2)) steps, where n is the order of the Elliptic Curve Group. Oct 24, 2013 CloudFlare uses elliptic curve cryptography to provide perfect forward secrecy which is essential for online privacy. First generation cryptographic algorithms like RSA and Diffie-Hellman are still the norm in most arenas, but elliptic curve cryptography is quickly becoming the go-to solution for privacy and security online. Provides a Cryptography Next Generation (CNG) implementation of the Elliptic Curve Diffie-Hellman (ECDH) algorithm. This class is used to perform cryptographic operations. ECDiffieHellmanCng Class (System.Security.Cryptography) Microsoft Docs. RSA offers the functionality of encrypting (short messages, or symmetric keys) with a public key, and decrypting with a private key. However, RSA key generation is extremely expensive, especially for 2048-bit+ keys. Is there an algorithm which employs elliptic curve cryptography, fast asymmetric encryption, fast key generation, and small keys.
The ECC (Elliptic Curve Cryptography) algorithm was originally independently suggested by Neal Koblitz (University of Washington), and Victor S. Miller (IBM) in 1985. Although the ECC algorithm was proposed for cryptography in 1985, it has had a slow start and it took nearly twenty years, until 2004 and 2005, for the scheme to gain wide acceptance. ECC (Elliptic Curve Cryptography) is a relatively new algorithm that creates encryption keys based on using points on a curve to define the public and private keys.
Key Benefits of ECC
ECC key is very helpful for the current generation as more people are moving to the Smartphone. As the utilization of Smartphone extends to grow, there is an emerging need for a more flexible encryption for business to meet with increasing security requirements.
Stronger Keys
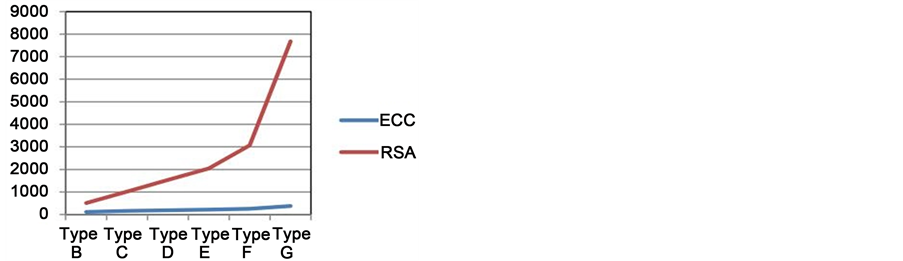
ECC stands for Elliptic Curve Cryptography is the latest encryption method offers stronger security. If we compare to the RSA and DSA algorithms, then 256-bit ECC is equal to 3072-bit RSA key. The reason behind keeping short key is the use of less computational power, fast and secure connection, ideal for Smartphone and tablet too.
The US government and the National Security Agency have certified ECC encryption method. The mathematical problem of the ECC algorithm, It is harder to break for hackers compare to RSA and DSA, which means the ECC algorithm ensures web site and infrastructure safety than traditional methods in a more secure manner.
Shorter Key Size
The elliptic curve cryptography (ECC) certificates allow key size to remain small while providing a higher level of security. ECC certificates key creation method is entirely different from previous algorithms, while relying on the use of a public key for encryption and a private key for decryption. By starting small and with a slow growth potential, ECC has longer potential lifespan. Elliptic curves are likely to be the next generation of cryptographic algorithms, and we are seeing the beginning of their use now.
| Minimum size (bits) of Public Keys | Key Size Ratio | |||
| Security (bits) | DSA / RSA | ECC | ECC to RSA / DSA | Valid |
| 80 | 1024 | 160-223 | 1:6 | Until 2010 |
| 112 | 2048 | 224-255 | 1:9 | Until 2030 |
| 128 | 3072 | 256-383 | 1:12 | Beyond 2031 |
| 192 | 7680 | 384-511 | 1:20 | |
| 256 | 15360 | 512+ | 1:30 | |
If we examine the above table, there is a considerable growth in DSA and RSA key than ECC key size. A longer key requires more space, more bandwidth, and additional processor power. Even, it will take a time to generate a key, encrypt data, and decrypt the data.
Why Elliptic Curve Cryptography is Required?
Encryption experts are pressed to find ever more effective methods, measured in security and performance, because the threats presented by hackers are ever greater – partly because the hackers themselves become more sophisticated in their attacks, and also because the fallout from an attack gets ever more dangerous as our use of data grows. It creates an urgency of new algorithms with a goal to provide a higher level of security by having keys that are more difficult to break, while offering better performance across the network and while working with large data sets.
Several factors are contributing to its increasing popularity. First of all, the security of 1024-bit encryption is degrading, due to faster computing and a better understanding and analysis of encryption methods. While brute force is still unlikely to crack 1024-bit encryption, other approaches, including highly intensive parallel computing in distributed computing arrays, are resulting in more sophisticated attacks. These attacks have reduced the effectiveness of this level of security. Even 2048-bit encryption is estimated by the RSA Security to be effective only until 2030.
- Web standards: Business owner has to mull over web server standards. Many web servers running on a single domain name can handle RSA, DSA, and ECC configuration. On the other side, few web servers do not have the ability to handle multiple algorithms and can utilize a single certificate on a single web server.
- Authentication speed: RSA, DSA, and ECC have diverse velocity for verification and authentication. RSA is a rapid algorithm in terms of client authentication while ECC is faster in terms of server authentication. Signature verification is rapidly in case of RSA key comparing to ECC key. There are transaction types, the processing power of the device; storage capacity, bandwidth, and consumption of power also influence the algorithm selection.
- Customer’s identity: Many government entities have started to accept DSA and ECC. They required for government subcontracts, government branches for their internal exchange of communication.
The number of connections plays a vital role in selecting algorithm standard. ECC can handle more connections at the same time compare to RSA algorithm. An Organization has to maintain the balance between security, user experience, and IT infrastructure cost involved in network process.
Get ECC Enabled SSL
To give true benefits of enhanced security, certificate authorities have started to embed ECC and DSA algorithm in their SSL certificates. Comodo has started to provide the ECC SSL certificates with keeping the emerging demand of Smartphone and other Compaq devices.
| If you are looking for ECC SSL certificate at affordable price then buy Comodo SSL certificate from us and get enhanced level security to your website. |
We are authorized reseller of Comodo that make your purchase worthful. You will get premium-class security with Comodo SSL certificates that will establish your brand reputation over the web.
secp256k1 refers to the parameters of the elliptic curve used in Bitcoin's public-key cryptography, and is defined in Standards for Efficient Cryptography (SEC) (Certicom Research, http://www.secg.org/sec2-v2.pdf). Currently Bitcoin uses secp256k1 with the ECDSA algorithm, though the same curve with the same public/private keys can be used in some other algorithms such as Schnorr.
Elliptic Curve Key Generation Algorithm Worksheet
secp256k1 was almost never used before Bitcoin became popular, but it is now gaining in popularity due to its several nice properties. Most commonly-used curves have a random structure, but secp256k1 was constructed in a special non-random way which allows for especially efficient computation. As a result, it is often more than 30% faster than other curves if the implementation is sufficiently optimized. Also, unlike the popular NIST curves, secp256k1's constants were selected in a predictable way, which significantly reduces the possibility that the curve's creator inserted any sort of backdoor into the curve.
Technical details
As excerpted from Standards:
Photoshop cs6 mac full download. The elliptic curve domain parameters over Fp associated with a Koblitz curve secp256k1 are specifiedby the sextuple T = (p,a,b,G,n,h) where the finite field Fp is defined by:
- p = FFFFFFFF FFFFFFFF FFFFFFFF FFFFFFFF FFFFFFFF FFFFFFFF FFFFFFFE FFFFFC2F
- = 2256 - 232 - 29 - 28 - 27 - 26 - 24 - 1
The curve E: y2 = x3+ax+b over Fp is defined by:
- a = 00000000 00000000 00000000 00000000 00000000 00000000 00000000 00000000
- b = 00000000 00000000 00000000 00000000 00000000 00000000 00000000 00000007
The base point G in compressed form is:
- G = 02 79BE667E F9DCBBAC 55A06295 CE870B07 029BFCDB 2DCE28D9 59F2815B 16F81798
and in uncompressed form is: Mixed in key 5 vip code generator mac.
- G = 04 79BE667E F9DCBBAC 55A06295 CE870B07 029BFCDB 2DCE28D9 59F2815B 16F81798 483ADA77 26A3C465 5DA4FBFC 0E1108A8 FD17B448 A6855419 9C47D08F FB10D4B8
Finally the order n of G and the cofactor are: Where can microsoft passport generate and store security keys.
- n = FFFFFFFF FFFFFFFF FFFFFFFF FFFFFFFE BAAEDCE6 AF48A03B BFD25E8C D0364141
- h = 01
Properties
- secp256k1 has characteristic p, it is defined over the prime field ℤp. Some other curves in common use have characteristic 2, and are defined over a binary Galois field GF(2n), but secp256k1 is not one of them.
- As the a constant is zero, the ax term in the curve equation is always zero, hence the curve equation becomes y2 = x3 + 7.
Elliptic Curve Key Length
See also
Elliptic Curve Key Generation Algorithm Download
- What does secp256k1 look like (Bitcoin stack exchange answer by Pieter Wuille)